IT Governance in the Financial Sector in Saudi Arabia
The Saudi Central Bank, formerly known as the Saudi Arabian Monetary Authority (SAMA), is the central bank of Saudi Arabia. It issued an IT governance framework on 12 December 2021 for financial institutions, including credit information companies and banks in Saudi Arabia. This framework aims to identify and resolve risks that are associated with IT and have an objective that is given below:
- To develop a unified approach for the member organizations so that they can easily deal with IT risks.
- To help the member organizations achieve a sufficient and mature level of IT controls.
- Ensure that information technology risks will be addressed adequately across all member organizations.
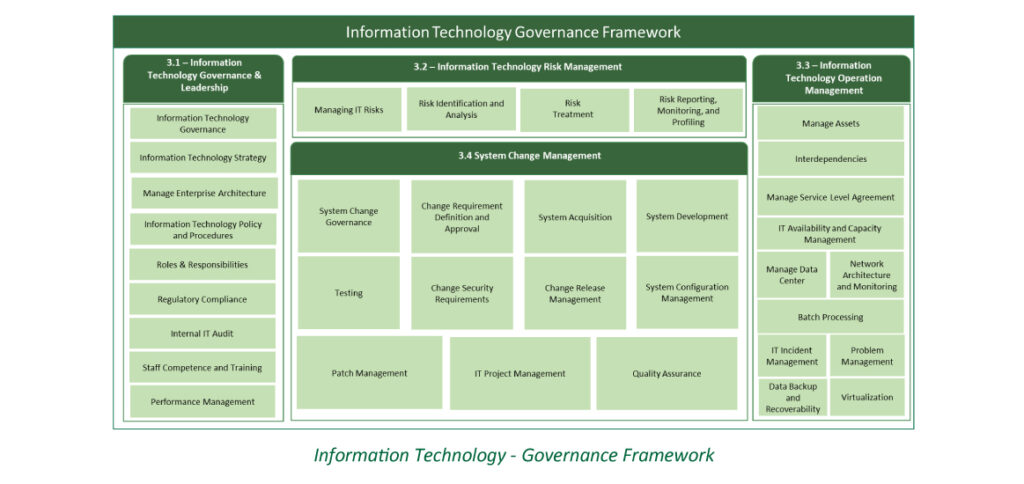
Overall, you can understand that this framework is designed as per the SAMA requirements and based on IT (information technology) standards. Apart from that, there are four main domains of the framework and various subdomains in which each subdomain has principle and control requirements.
Also, the framework confirms that member organizations should self-assess their compliance on a regular basis, and SAMA can further use these results to establish their maturity level using a six-level model. One can even get an insight or complete knowledge about the principles and controls, including domains and subdomains.
Scope of the Framework
The framework includes objectives and principles to define, implement, maintain, monitor, and enhance IT governance controls throughout SAMA-regulated member organizations. It also specifies rules to control IT governance and makes it easy for the members’ organizations to apply the rules to information assets. Furthermore, the framework outlines IT governance responsibilities for member organizations, third parties, customers, employees, and subsidiaries.
It is even necessary to implement the framework in conjunction with SAMA’s business continuity framework and cyber security because the framework has been linked to numerous corporate policies, such as staff training and change management. And it is specifically designed for business owners, CIOs, information assets owners, senior and executive management, and those people who want to define, implement, and review IT controls within the member organizations.

Besides the owner of this framework, SAMA aims to provide interpretations for the control requirements and principles. It has also set a period to review the framework and make the framework effective. Additionally, SAMA will focus on IT risks and threats and ensure to address them carefully. SAMA will also update the framework if it is requested by the member organization, and the changes will be made as per the requirement of the newest version.
What is a Principle & the Control Requirements?
A principle is defined as the main set of necessary IT controls associated with the subdomain. Whereas the control requirements are those requirements in which it is crucial to consider the IT controls as a mandatory option.
Structure of the Framework
As discussed above, the structure of the framework is divided into four domain, and that is as follow:
- Information technology governance and leadership
- Information technology operations management
- Information technology risk management
- System change management
-
Information Technology Governance and Leadership
It is the responsibility of the member organization’s board to set the IT (information technology) governance along with assuring the management of IT risks effectively within the member organization. Moreover, the organisation’s board members can allocate their responsibilities in the IT governance sector to ITSC (IT steering committee) and the senior management. The ITSC can also take responsibility for creating IT strategies for the member organizations and define the IT governance.
What is the Principle of IT Governance & Its Control Requirements?
As a principle, the framework states that the structure of an IT governance should be clearly defined, authorized, and maintained with sufficient resources. This process helps monitor and control the overall member organizations’ approach to IT. With the help of best practices, the IT strategy can easily align with the member organisations’ strategic objectives and comply with legal and regulatory requirements.
Control Requirements
- Establish an ITSC by member organizations, and it should be mandated by the board.
- The ITSC should be directed by senior management who will manage the operations of Member Organizations.
- An ITSC charter is prepared, accepted, and includes the following:
- Roles & responsibilities
- Committee objectives
- The meeting must be held on a quarterly basis.
- Minimum number of meeting participants
- Decisions and meeting minutes must be documented and retained.
- The member organizations should organize formal IT-related practices to manage financial activities, including cost and budget. The spending can also prioritize and align with IT strategies, and the overall IT budget should be adjusted, monitored, and reviewed based on the specific business needs.
2. Information Technology Operations Management
The ITOM (IT operations management) manages the cost, provisioning, performance, capacity, data centers, and security. It is suitable to check the availability of services and infrastructure, including public cloud resources and private cloud deployments. The operations management of IT can even be defined as a function. This function ensures the consistent maintenance and management of the members’ organization and helps in offering the agreed-upon level of IT services. Apart from that, the member organizations must address the risk factors that are associated with IT (information technology) operations.
What is the Principle of IT Governance & Its Control Requirements?
By maintaining up-to-date and accurate inventory, a principal asset management process should be established to help the members’ organization gain visibility about information assets.
Control Requirements
The control requirements for the asset management include the following:
- The process of asset management should be defined, approved, executed, and communicated.
- The asset management process’s effectiveness should be measured, monitored, and evaluated periodically.
- The process of asset management involves several options, such as asset onboarding, asset classification, identification, labelling, handling, disposal, and decommissioning.
3. Information Technology Risk Management
According to the principle of IT risk management, processes should be designed, approved, communicated and aligned with the enterprise risk management of the member organization. This process begins with the identification, research, treatment, tracking, and evaluation of IT risks at suitable intervals.
Control Requirements
The control requirements for IT risks management are as follows:
- The process of IT risk management should be defined, implemented, approved, and communicated.
- The procedures should be measured and evaluated periodically to ensure the effectiveness of IT risks.
- The process of IT risk management needs to align with the member organization’s enterprise risk management process.
4. System Change Management
According to the framework, system change management is a process of defining, designing, implementing, testing, and making modifications related to information assets. Make sure this process should not be limited to data, device, application, and software. Otherwise, it would be difficult for the member organizations to resolve risks that may relate to the system change management.




